AZ-104 Deep Dive: Dynamic Membership in Microsoft Entra ID
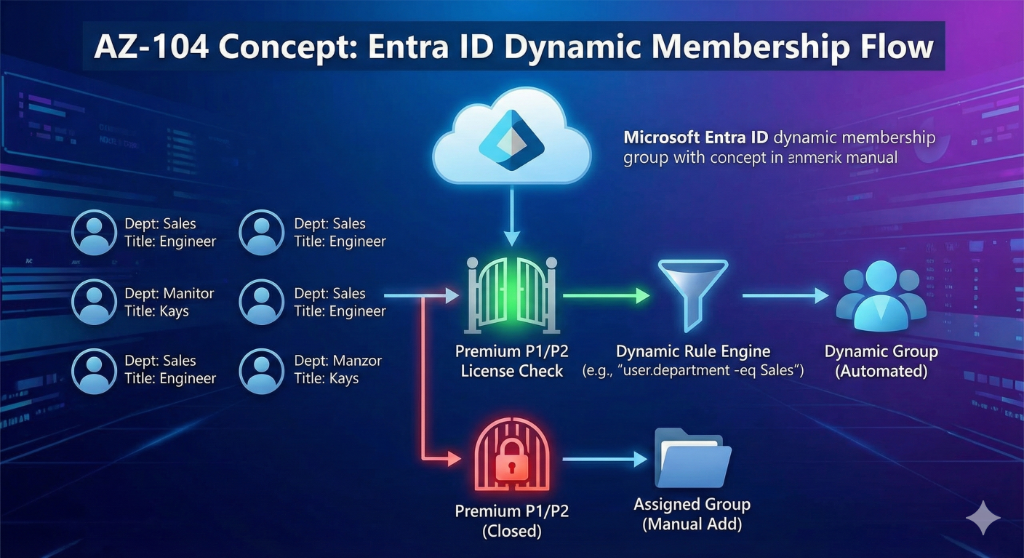
Custom Diagram
In Lab 01 - Manage Microsoft Entra ID Identities, one of the most critical tasks - and a frequent stumbling block on the actual exam - is configuring Dynamic Groups.
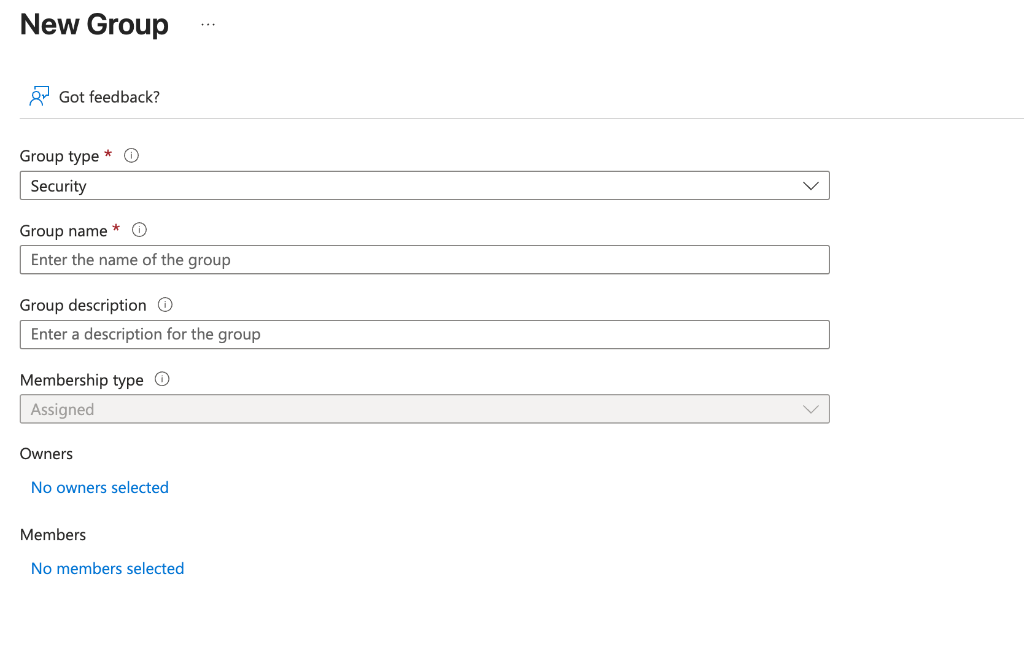
While creating a standard "Assigned" group is straightforward, Dynamic Membership introduces automation based on user or device attributes. However, before you even write your first query, there is a strict prerequisite that Microsoft loves to test you on.
1. The Critical Exam "Gotcha": Licensing
You cannot configure Dynamic Membership with the default "Free" tier of Microsoft Entra ID (formerly Azure AD).
An Entra ID Premium P1 or P2 license is required for Dynamic Membership.
If you are in the Azure Portal and the "Membership type" dropdown is grayed out or missing the "Dynamic User" option, it is almost always because the tenant lacks a Premium license.
2. Dynamic Membership Types
When configuring a group in Entra ID, you will encounter three membership types. For AZ-104, you must understand the difference between the two dynamic options:
Assigned
You manually select users or devices to add to the group.
Ad-hoc teams, temporary project groups (e.g., "Project Alpha Team").
Dynamic User
Users are added/removed automatically based on attributes.
All employees in a specific department or location.
Dynamic Device
Devices are added/removed automatically based on attributes.
Applying Intune policies to all Windows 10 machines.
3. Creating the Rule (Lab 01 Context)
In the lab, you are often asked to create a group (e.g., IT-Cloud-Admins) that automatically includes anyone with the Job Title "Cloud Engineer".
The Syntax
Entra ID uses a specific expression language for these rules.
-
Simple Rule:
(user.jobTitle -eq "Cloud Engineer") -
Complex Rule:
(user.department -eq "IT") and (user.city -eq "Mississauga")
Key Rules for the Exam:
- Scope: A dynamic group can contain either users or devices, generally not both in the same rule logic (though the scope is defined by the "Membership type" dropdown selected earlier).
- Latency: Membership updates are not instant. It can take minutes (or longer in large tenants) for the background process to evaluate the rule and update the group members.
- Cannot Manually Add: You cannot manually "Add Member" to a Dynamic Group. The only way to get in is to match the rule.
4. Summary Checklist for AZ-104
If you see a question about automating group membership, remember:
- License Check: Do we have Premium P1/P2?
- Attribute Accuracy: Does the user's attribute (e.g.,
Department) match the rule exactly? (Watch out for typos or case sensitivity in values). - Automation: This removes administrative overhead - users are automatically removed from the group if their attribute changes (e.g., they move from "Sales" to "HR").
Want to discuss this further?
I'm always happy to chat about cloud architecture and share experiences.
Follow me for more insights on cloud architecture and DevOps
Follow on LinkedIn